Les Bell
Blog entry by Les Bell
Welcome to today's daily briefing on security news relevant to our CISSP (and other) courses. Links within stories may lead to further details in the course notes of some of our courses, and will only be accessible if you are enrolled in the corresponding course - this is a shallow ploy to encourage ongoing study. However, each item ends with a link to the original source.
News Stories
ISS Leaking - But Not in the Way You Think
Via New Scientist comes the strange story of a leak on the International Space Station (ISS). In this case, there's no hiss of escaping air - it's data that is leaking.
Pseudonymous security researcher Gi7w0rm, in hot pursuit of a space-related vulnerability in a "sensitive" government system, accidentally discovered an open telemetry feed which provides a continuous stream of all kinds of interesting, and some not-so-interesting, information about the status of various systems on the ISS: battery charger assemblies, antenna alignments, and, most curiously, the status of the unit that processes urine into potable water:
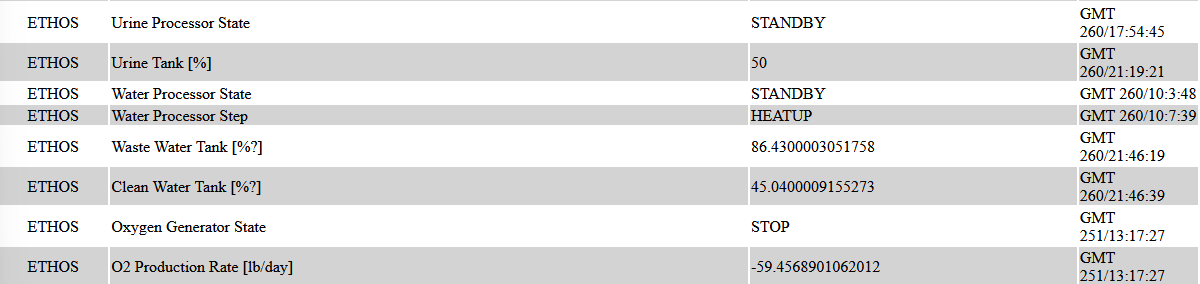
The feed is viewable at https://iss-mimic.github.io/Mimic/. So now you can see whenever an astronaut takes a leak.
NASA has not commented at this time, but a Boeing engineer has stated that the feed is an obsolete component of a now-defunct web site called ISSLive. While the project was abandoned, this stream lives on, providing a small subset of the thousands of telemetry channels used by the ISS.
The lesson for us: this is a classic example of Improper Web API Asset Management: a failure to retire an old version of an API that is no longer in use. Fortunately, in this case, no particularly sensitive information is exposed.
Sparkes, Matthew, Data leak means anyone can see when astronauts urinate on the ISS, New Scientist, 15 September 2023. Available online at https://www.newscientist.com/article/2392360-data-leak-means-anyone-can-see-when-astronauts-urinate-on-the-iss/.
CoinEx Crypto Theft Down to Lazarus Group, Say Analysts
Being the subject of extremely tight financial sanctions, North Korea has long resorted to cybercrime as a source of hard currencies, and the growth of cryptocurrencies has only accelerated this process. In a period of just over three months, the most prolific North Korean APT, Lazarus Group, has been identified as behind theft of almost $US240 million of cryptocurrency from Atomic Wallet ($US100 million) CoinsPaid ($US37.3 million), Alphapo ($US60 million), and Stake.com ($US41 million).
Despite the widespread assumption that cryptocurrency transactions are anonymous, blockchain analysis performed by several analysis firms can trace the flow of funds through wallets and mixers, making it possible to link different breaches to the same actors and attribute them with some confidence. Now, reports from two companies attribute the latest breach, at CoinEx on 12 September, to Lazarus Group with a high degree of confidence. At this stage, CoinEx has not identified all the affected wallets, but the total value of the theft is estimated to be around $US54 million.
In these thefts, Lazarus Group has employed a strategy of switching funds between blockchains as well as converting stolen funds into Ethereum before transferring them onwards. However, this is not enough to stop analysts from tracing the funds.
Certik, Lazarus Group's Web3 Rampage, blog post, 13 September 2023. Available online at https://www.certik.com/resources/blog/216tegKHtRmx5pOI3UgYCX-lazarus-groups-web3-rampage.
Elliptic Research, How the Lazarus Group is stepping up crypto hacks and changing its tactics, blog post, 15 September 2023. Available online at https://www.elliptic.co/blog/how-the-lazarus-group-is-stepping-up-crypto-hacks-and-changing-its-tactics.
Dymocks Customer Data Stolen From External Supplier
Last week, we revealed the theft of the personal information of Dymocks' customers by a ransomware operator, and a threat to publish this data on the dark web.
The company has now confirmed that customer records have been placed on the dark web, but states that the breach was achieved by the compromise of a business partner's systems:
"Although our investigations are ongoing, we do believe that one of our third-party partner’s systems were subject to unauthorised access. Whilst we continue to keep all avenues open, we are working with the identified partner to focus on understanding if and how their systems were accessed despite their security measures."
Approximately 1.24 million customer contact records have been released. Dymocks also states that there is no evidence of any unauthorized access to its own systems. This is just the latest in a long series of breaches in which smaller suppliers expose the data of their larger clients and partners.
Dymocks, Frequently Asked Questions (FAQs) – Dymocks Data Incident, customer notice, 15 September 2023. Available online at https://www.dymocks.com.au/customer-notices.
Upcoming Courses
- SE221 CISSP Fast Track Review, Virtual/Online, 13 - 17 November 2023
- SE221 CISSP Fast Track Review, Sydney, 4 - 8 December 2023
These news brief blog articles are collected at https://www.lesbell.com.au/blog/index.php?courseid=1. If you would prefer an RSS feed for your reader, the feed can be found at https://www.lesbell.com.au/rss/file.php/1/dd977d83ae51998b0b79799c822ac0a1/blog/user/3/rss.xml.
![]()
 Copyright to linked articles is held by their individual authors or publishers. Our commentary is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License and is labeled TLP:CLEAR.
Copyright to linked articles is held by their individual authors or publishers. Our commentary is licensed under a Creative Commons Attribution-ShareAlike 4.0 International License and is labeled TLP:CLEAR.